BLOG
fdxmz24: Understanding the Significance and Applications

One such term that has sparked curiosity is FDXMZ24. While it may appear as a random alphanumeric combination, it has the potential to symbolize a new technological trend, encryption standard, or digital security framework.
This article explores the possible meanings and applications of FDXMZ24, its relevance in the modern digital ecosystem, and its impact on security, innovation, and industry trends.
Decoding FDXMZ24: What Could It Represent?
FDXMZ24 could be interpreted in several ways, depending on its application in different fields. Some of the possible meanings include:
1. Cybersecurity and Encryption
FDXMZ24 could represent a new encryption algorithm, authentication protocol, or security key. In cybersecurity, strong alphanumeric combinations are often used in encryption keys and hashing algorithms to enhance data protection.
Potential uses in cybersecurity:
- Advanced encryption standards (AES): FDXMZ24 could be part of a new cryptographic standard for securing sensitive information.
- Multi-factor authentication (MFA): It might serve as a unique security code for accessing high-security systems.
- Blockchain technology: A decentralized security framework could integrate FDXMZ24 to enhance transaction validation.
2. Artificial Intelligence and Machine Learning
AI and ML models rely on complex datasets and identifiers to train neural networks. FDXMZ24 might be a model identifier used in deep learning research, AI-powered applications, or an experimental technology in natural language processing (NLP).
Possible AI applications:
- Neural network training: FDXMZ24 could be a dataset name for training AI in pattern recognition.
- Computer vision projects: Used in facial recognition or autonomous systems to identify and process data.
- AI-driven security tools: A new AI-powered framework for detecting cyber threats could integrate FDXMZ24 as an identifier.
3. Cloud Computing and Digital Infrastructure
As businesses migrate to cloud-based solutions, unique identifiers are assigned to servers, databases, and software applications. FDXMZ24 might be a server code, database encryption key, or software version name within cloud infrastructure.
Possible cloud computing applications:
- Cloud-based authentication: A security token for cloud login and encryption.
- Distributed computing systems: An identifier in large-scale cloud computing networks.
- Data encryption protocols: Used in securing enterprise-level data centers and hybrid cloud environments.
4. Software Development and Programming
In software development, alphanumeric codes like FDXMZ24 are used as unique project identifiers, API keys, or software patches. It could belong to an open-source project, private software release, or an advanced development tool.
Possible software development uses:
- API authentication key: Used for securing API transactions in web and mobile applications.
- Software version identifier: A unique code for identifying different software releases or patches.
- Programming libraries and frameworks: A reference number for an emerging coding framework.
5. Internet of Things (IoT) and Smart Technology
With the rise of IoT, billions of devices require unique identification codes for network communication. FDXMZ24 might be a device ID, firmware update version, or IoT security key.
Potential IoT applications:
- Smart home security: A unique identifier for smart locks, cameras, and IoT-enabled devices.
- Industrial IoT networks: Used to track smart manufacturing equipment and automation systems.
- Wearable technology: A code for a next-gen smartwatch, fitness tracker, or medical device.
The Importance of Secure Identifiers Like FDXMZ24
In digital security, alphanumeric identifiers serve as an essential component for authentication, cryptography, and secure data exchanges. With cyber threats increasing, organizations must implement unique and complex security keys like FDXMZ24 to prevent unauthorized access.
Why Secure Identifiers Matter?
- Data Protection: Prevents data breaches by securing access to sensitive information.
- Authentication & Verification: Ensures only authorized users can access systems and networks.
- Secure Online Transactions: Prevents fraud in e-commerce, banking, and financial services.
- Blockchain & Cryptography: Enhances security in decentralized applications and digital assets.
The Future of Digital Security and Innovation with FDXMZ24
As digital transformation accelerates, the need for advanced security measures, AI-driven frameworks, and cloud-based solutions will continue to grow. FDXMZ24, whether an encryption standard, AI model, or software identifier, could play a vital role in the next wave of technological evolution.
Potential Future Applications:
- Next-gen cybersecurity algorithms to combat cyber threats.
- AI-powered authentication for biometric security.
- Enhanced blockchain security for decentralized finance (DeFi) and NFT marketplaces.
- IoT-driven smart infrastructure for secure and connected cities.
Conclusion
FDXMZ24, while seemingly a random alphanumeric sequence, holds potential significance in cybersecurity, AI, cloud computing, IoT, and software development. Whether representing a secure encryption key, AI model identifier, or cloud computing resource, such identifiers play a crucial role in modern digital infrastructure.
As we move towards a future driven by technology, identifiers like FDXMZ24 could be at the core of securing data, enhancing AI models, and enabling seamless cloud-based operations. The digital world is evolving, and secure, innovative solutions will continue to shape the way we interact with technology.
BLOG
Unveiling the World of Breezy News: Your Go-To Source for Fresh Updates

Introduction
In a world where information moves faster than ever, finding a reliable and easy-to-consume news source is essential. Breezy News has emerged as a modern platform designed to deliver fresh updates in a quick, accessible, and engaging way. Whether you are looking for breaking news, local updates, or trending stories, Breezy News aims to keep you informed without overwhelming you.
What is Breezy News?
Breezy News is a digital-first news platform that focuses on providing concise, timely, and reader-friendly content. Unlike traditional outlets that may present lengthy reports, Breezy News emphasizes clarity and speed, making it ideal for modern audiences.
Core Focus Areas
- Breaking news updates
- Local and community stories
- Trending topics
- Lifestyle and human-interest content
- Quick-read articles
How Breezy News Works
The platform is built around simplicity and accessibility.
Content Delivery
Articles are designed to be short, informative, and easy to read on mobile devices.
Real-Time Updates
News is published quickly to keep readers informed about current events.
Digital Accessibility
Users can access content through:
- Websites
- Social media platforms
- Mobile-friendly interfaces
Key Features of Breezy News
1. Fast and Fresh Updates
Breezy News focuses on delivering news as it happens, ensuring readers stay current.
2. Easy-to-Read Format
Short paragraphs and simple language make content accessible to all readers.
3. Wide Content Variety
From local updates to global trends, the platform covers diverse topics.
4. Mobile Optimization
Designed for users who consume news on smartphones and tablets.
Why Breezy News is Gaining Popularity
Several factors contribute to its growing appeal:
- Quick and digestible content
- Focus on relevant and trending topics
- Strong presence on social media
- User-friendly reading experience
In an age of information overload, platforms like Breezy News provide a refreshing alternative.
Role in Modern Digital Media
Breezy News reflects the shift toward:
- Short-form journalism
- Real-time reporting
- Audience-focused storytelling
It aligns with how modern readers prefer to consume news—quickly, clearly, and on-the-go.
Benefits of Using Breezy News
Saves Time
Readers can stay informed without reading lengthy articles.
Easy Accessibility
Available across multiple devices and platforms.
Engaging Content
Designed to keep readers interested and informed.
Community Connection
Often highlights local stories that matter to readers.
Challenges Facing Platforms Like Breezy News
Despite its advantages, there are challenges:
- Balancing speed with accuracy
- Competing with larger media outlets
- Avoiding misinformation in fast reporting
- Maintaining credibility
Successful platforms must ensure fact-checking and responsible journalism.
How to Get the Most Out of Breezy News
To use the platform effectively:
- Follow official pages for updates
- Cross-check important news with reliable sources
- Engage with content for better recommendations
- Stay aware of trending topics
Conclusion
Breezy News represents the future of digital journalism—fast, accessible, and reader-focused. With its emphasis on fresh updates and simplified storytelling, it has become a go-to source for modern news consumers.
FAQ’s
1. What is Breezy News?
Breezy News is a digital news platform that provides quick and easy-to-read updates on current events and trending topics.
2. Is Breezy New’s reliable?
It aims to provide timely information, but readers should verify important news from multiple trusted sources.
3. What type of content does Breezy New’s cover?
It covers breaking news, local updates, lifestyle topics, and trending stories.
4. How can I access Breezy New’s?
You can access it through its website, social media platforms, and mobile devices.
5. Why is Breezy New’s popular?
Its short, engaging, and mobile-friendly content makes it appealing to modern readers.
BLOG
Unraveling the Mysteries of Chainiste: A Comprehensive Guide

Introduction
The term Chainiste is not widely defined in mainstream dictionaries, yet it has begun appearing in various online discussions, niche communities, and conceptual frameworks. Whether used in technology, philosophy, or branding, Chainiste carries an air of mystery that sparks curiosity.
This guide explores what Chainiste could mean, where it might come from, and how it is being interpreted in modern contexts.
What is Chainiste?
At its core, Chainiste appears to be a conceptual or emerging term rather than a strictly defined word. It is often interpreted in multiple ways depending on context.
Possible Interpretations
- A person or system connected to chains or networks
- A philosophy centered on interconnected systems
- A digital or blockchain-related concept
- A brand or identity built around connectivity
Because the term lacks a fixed definition, it is considered flexible and evolving.
Etymology and Origins
The word “Chainiste” likely derives from:
- “Chain” – representing connection, sequence, or linkage
- “-iste” – a suffix often used to describe a follower, specialist, or practitioner
Together, the term could suggest “one who works with or believes in chains or interconnected systems.”
Chainiste in Technology
One of the most common interpretations of Chainiste is in the tech world, especially linked to Blockchain.
Possible Tech Meanings
- A blockchain enthusiast or expert
- A developer working with decentralized systems
- A supporter of distributed ledger technology
In this sense, a Chainiste might represent someone deeply involved in modern digital infrastructure and decentralized innovation.
Chainiste as a Philosophy
Beyond technology, Chainiste can also be viewed as a philosophical concept.
Core Ideas
- Everything is interconnected
- Actions create chains of consequences
- Systems influence one another continuously
This aligns with broader ideas found in systems thinking and network theory.
Chainiste in Digital Culture
In online communities, Chainiste may be used as:
- A username or identity
- A niche community label
- A conceptual brand name
It reflects modern internet culture where new terms emerge organically and gain meaning through usage rather than formal definition.
Applications of the Chainiste Concept
1. Technology & Innovation
Used to describe professionals working in blockchain or network systems.
2. Business & Branding
Companies may adopt the term to represent connectivity and modern thinking.
3. Philosophy & Thought Leadership
Represents interconnected thinking and systemic awareness.
4. Creative Fields
Writers and creators may use it symbolically to represent relationships and continuity.
Why Chainiste is Gaining Attention
Several factors contribute to its rising interest:
- Growth of blockchain and decentralized systems
- Increased focus on interconnected digital ecosystems
- Curiosity around unique and modern terminology
- Branding appeal due to its futuristic tone
Challenges in Defining Chainiste
Despite its appeal, the term faces limitations:
- No official or standardized definition
- Multiple interpretations leading to confusion
- Lack of academic or institutional recognition
This makes it more of a conceptual keyword than a formal term.
Future of Chainiste
The future of Chainiste depends on how it is adopted:
- It could become a recognized term in tech communities
- It may evolve into a brand or movement
- It could remain a niche concept with flexible meaning
Like many modern digital terms, its value lies in how people use and define it over time.
Conclusion
Chainiste is a fascinating example of how language evolves in the digital age. Whether viewed through the lens of Blockchain, philosophy, or branding, it represents the idea of connection and interconnected systems.
FAQ’s
1. What does Chainiste’s mean?
Chainiste’s is an emerging term often associated with interconnected systems, blockchain, or conceptual philosophies.
2. Is Chainiste a real word?
It is not officially defined in dictionaries but is used in niche and digital contexts.
3. Is Chainiste related to blockchain?
Yes, it is often interpreted as being connected to blockchain and decentralized technologies.
4. Can Chainiste be used as a profession?
Informally, it could describe someone working with network systems or blockchain technologies.
5. Why is Chainiste gaining popularity?
Its modern, flexible meaning and connection to digital innovation make it appealing in online communities.
BLOG
Vivek Mehra: A Visionary Leader’s Journey

Introduction
Vivek Mehra stands out as a dynamic leader whose career spans corporate leadership, entrepreneurship, education, and thought leadership. His journey reflects a blend of innovation, resilience, and a deep commitment to knowledge dissemination—making him a notable figure in the global publishing and education ecosystem.
Early Life and Educational Foundation
While detailed early-life records are limited publicly, Vivek Mehra’s academic and professional path reflects a strong foundation in business, leadership, and intellectual pursuits. His later engagement with law studies and a PhD in management highlights his continuous dedication to learning and growth.
Rise in Corporate Leadership
Leadership at SAGE Publications India
One of the most defining phases of his career was his role as:
- CEO and Managing Director
- Later Chairman
At SAGE Publications India, he played a key role in expanding academic publishing, fostering global collaborations, and strengthening access to scholarly content. His leadership contributed significantly to enhancing the reach of research publications in emerging markets.
Entrepreneurial Vision
Founder of Vikramshila Research Pvt Ltd
After a successful corporate career, Vivek Mehra transitioned into entrepreneurship by founding Vikramshila Research in 2023.
Key Goals of the Venture:
- Promote open-access research publishing
- Support scholars from developing countries
- Contribute to building a “knowledge-driven society”
This move highlights his vision of democratizing knowledge and making academic research more accessible worldwide.
Contributions Beyond Business
Thought Leadership and Mentorship
Vivek Mehra is more than a corporate executive. His contributions include:
- TEDx speaker, sharing insights on leadership and innovation
- Startup mentor, guiding emerging entrepreneurs
- Workshop trainer, focusing on publishing and ethics
Academic Engagement
He actively teaches research publishing and ethics to PhD students and continues to pursue his own doctoral studies, demonstrating his lifelong commitment to education.
Awards and Recognitions
His impactful work has earned him multiple accolades:
- Business Excellence and Innovative Best Practices Academia Award (2019)
- Sharda Top Rankers Excellence Award for Visionary Leadership (2016)
- Vijayshree Award (Government of Maharashtra, 1994) for simplifying agricultural technology
These awards reflect his contributions across industries—from publishing to technology and education.
Leadership Style and Philosophy
Key Traits
- Vision-driven thinking: Focused on long-term impact rather than short-term gains
- Commitment to learning: Continuously evolving through education and research
- People-centric leadership: Known for building teams and nurturing talent
He describes himself as a “rational optimist,” emphasizing balanced thinking and continuous discovery.
Impact on Publishing and Education
Vivek Mehra’s influence extends into:
- Expanding academic publishing in emerging economies
- Promoting ethical research practices
- Supporting global knowledge exchange
His work bridges the gap between traditional publishing and modern digital dissemination.
Personal Interests
Beyond his professional life, he is known for:
- Practicing yoga and squash
- Exploring philosophy and intellectual thought
- Writing and sharing perspectives through blogs
These interests contribute to his well-rounded leadership approach.
Challenges and Growth
Like many visionary leaders, Vivek Mehra’s journey includes:
- Navigating the shift from traditional to digital publishing
- Building a startup after a long corporate career
- Adapting to evolving global education systems
His ability to embrace change has been a key factor in his success.
Legacy and Future Outlook
With initiatives like Vikramshila Research, Vivek Mehra continues to:
- Champion open knowledge ecosystems
- Inspire future leaders and scholars
- Shape the future of global publishing
His journey reflects a commitment to making knowledge accessible and impactful on a global scale.
FAQ’s
1. Who is Vivek Mehra?
Vivek Mehra is an Indian publishing executive, entrepreneur, and founder of Vikramshila Research, known for his contributions to academic publishing.
2. What is Vivek Mehra known for?
He is best known for his leadership at SAGE Publications India and his work in promoting open-access research.
3. What is Vikramshila Research?
It is a research publishing platform founded by Vivek Mehra to make scholarly content accessible globally.
4. Has Vivek Mehra received any awards?
Yes, he has received multiple awards, including the Business Excellence Award and the Vijayshree Award.
5. Is Vivek Mehra involved in education?
Yes, he teaches research publishing and ethics and is pursuing a PhD in management.
6. What is his leadership style?
He is known for visionary, people-centric, and learning-driven leadership.
7. What is his current focus?
He is focused on expanding open-access publishing and mentoring the next generation of leaders.
Conclusion
Vivek Mehra exemplifies what it means to be a visionary leader in the modern era. From corporate success to entrepreneurial innovation, his journey highlights the power of knowledge, leadership, and continuous growth.
-

 TECH1 year ago
TECH1 year agoHow Cyber Security Services Help Organizations Manage Cyber Risk
-

 BLOG1 year ago
BLOG1 year agoSlothokiturbo.net: Exploring the World of Online Gaming and Community
-

 BLOG1 year ago
BLOG1 year agoLiteroticatags: Exploring the World of Erotica and Its Online Community
-

 TECHNOLOGY1 year ago
TECHNOLOGY1 year agoAagmal: The Future of Innovation and Efficiency
-

 BLOG1 year ago
BLOG1 year agoErothtos: Understanding Its Role in Today’s World 2025
-

 BLOG1 year ago
BLOG1 year agoWatchmenontheall Calvin: An Exploration of Themes, Characters, and Significance
-
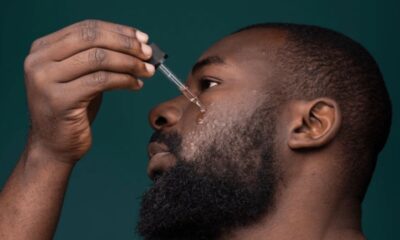
 FASHION12 months ago
FASHION12 months agoAchieve the Perfect Beard with Black Male Beard Products
-

 TECH1 year ago
TECH1 year agoMansrufer: Pioneering Progress in Technology
