BLOG
Watchmenontheall Calvin: An Exploration of Themes, Characters, and Significance

Imagine a story that weaves together the threads of morality, sacrifice, and justice, all tied into a single narrative fabric that seems to intensify with every turn of the page. Watchmenontheall Calvin is one such masterpiece. A tale that goes beyond mere storytelling, it beckons its readers to question values, explore character depths, and unlock the subtle significance behind its gripping themes.
Whether you’re a long-time admirer of richly layered narratives or a curious newcomer intrigued by the enigma of Watchmenontheall Calvin, this guide will take you into the heart of its brilliance. We’ll uncover recurring themes, dissect its unforgettable characters, and marvel at the enduring significance of this work.
Themes in Watchmenontheall Calvin: The Soul of the Story
Every story worth its weight in ink is built upon its themes—the ideas it explores, the questions it raises, and the morals it imparts. Watchmenontheall Calvin fearlessly dives into profound topics, presenting themes that resonate long after the final word has been read.
The Fragility of Justice
At its core, the narrative investigates the delicate balance between right and wrong. Justice, in this world, feels more like a trembling tightrope act than a foundational pillar. Through its twists and conflicts, the story compels readers to reconsider the concept of fairness and whether it is truly impartial or inherently subjective.
Sacrifice and Redemption
Few themes are as poignant as sacrifice. Watchmenontheall Calvin masterfully illustrates how its characters wrestle with decisions that demand they give up something integral—be it safety, love, or integrity—for the greater good. Yet, each sacrifice is not without the promise (or illusion) of redemption, a constant undercurrent that gives hope amidst despair.
The Mask of Morality
A striking exploration in Watchmenontheall Calvin lies within its dissection of morality. It challenges readers to reflect on who decides what is moral and unmasks the fine line between heroic and villainous actions. Are the characters saviors clad in righteousness or flawed individuals driven by self-interest?
Unforgettable Characters and Their Depths
Watchmenontheall Calvin would not hold its weight without its rich tapestry of characters, each a mirror reflecting the best and worst of human nature. These individuals give life to the themes, influencing the narrative in compelling and unpredictable ways.
Calvin – The Reluctant Watchman
Calvin embodies the reluctant hero archetype, yet he is anything but a cliché. Haunted by his past decisions, Calvin is a man at war with himself. He wields power not as a privilege but as a burden, his every action teetering between the drive to protect and the temptation to control.
Despite his internal conflicts, Calvin is a character that demands empathy. His struggles mirror the universal human desire to do good, even when the boundaries of goodness blur beyond recognition.
Mira – The Unyielding Idealist
Mira’s strength lies in her unshakable belief in a brighter future. She emerges as a light amidst the shadows of moral ambiguity, challenging Calvin and others to question their motives. Her character demonstrates that hope and idealism are not weaknesses but invaluable strengths in a fractured world.
The Faceless Order – Guardians or Overlords?
An enigmatic presence in the story, the Faceless Order wields immense influence, but at what cost? They are the manifestation of an age-old moral debate—does the end justify the means? Their calculated decisions and concealed motives add layers of intrigue, making their presence a thought-provoking element within the narrative.
The Significance of Watchmenontheall Calvin
Why does Watchmenontheall Calvin hold such a special place among its readers? Its significance lies not just in the story it tells, but in the questions it leaves behind. This is a tale that transcends its fictional boundaries, nudging you to reflect on your own values and the shades of gray that permeate everyday life.
Impact on Art and Literature
The work exemplifies how art and storytelling can intersect to create something profound. Watchmenontheall Calvin strikes a delicate balance between entertainment and introspection. It’s a narrative that doesn’t just demand your attention—it invites your participation.
A Reflection of Humanity
More than just a book, Watchmenontheall Calvin serves as a mirror, reflecting humanity’s complexities. It holds space for hope, tragedy, grit, and grace—all encapsulated within the challenges its characters face.
A Need for Vigilance
The title itself, Watchmenontheall Calvin, reminds readers of the importance of vigilance—not merely in combating external threats but in confronting internal certainties. It’s a quiet reminder that we must carefully watch over more than walls; we must also guard our intentions, beliefs, and ideals.
How to Unlock New Insights
Whether you’re a seasoned reader revisiting its pages or someone exploring this story for the first time, here are practical ways to discover fresh insights from Watchmenontheall Calvin:
- Re-read Through a Thematic Lens: Revisit the story with one of its central themes in mind. Consider how justice or morality evolves from beginning to end.
- Focus on a Single Character’s Arc: How does Calvin or Mira grow throughout the story? Notice their subtle transformations and pivotal moments.
- Discuss it With Fellow Enthusiasts: Sometimes, the best insights come from shared conversations. Join a forum or book club to hear diverse interpretations.
What Does Watchmenontheall Calvin Mean to You?
Few stories leave a lasting imprint the way Watchmenontheall Calvin does. It doesn’t just offer a storyline—it extends a hand, inviting readers to grapple with the big questions and step closer to understanding themselves through the lens of fictional characters.
If you’ve yet to experience the layers of Watchmenontheall Calvin, now is the perfect time to change that. Open your mind to the intricate worlds within its pages. After all, who watches over the boundaries of your heart and mind but you?

BLOG
Unveiling the World of Breezy News: Your Go-To Source for Fresh Updates

Introduction
In a world where information moves faster than ever, finding a reliable and easy-to-consume news source is essential. Breezy News has emerged as a modern platform designed to deliver fresh updates in a quick, accessible, and engaging way. Whether you are looking for breaking news, local updates, or trending stories, Breezy News aims to keep you informed without overwhelming you.
What is Breezy News?
Breezy News is a digital-first news platform that focuses on providing concise, timely, and reader-friendly content. Unlike traditional outlets that may present lengthy reports, Breezy News emphasizes clarity and speed, making it ideal for modern audiences.
Core Focus Areas
- Breaking news updates
- Local and community stories
- Trending topics
- Lifestyle and human-interest content
- Quick-read articles
How Breezy News Works
The platform is built around simplicity and accessibility.
Content Delivery
Articles are designed to be short, informative, and easy to read on mobile devices.
Real-Time Updates
News is published quickly to keep readers informed about current events.
Digital Accessibility
Users can access content through:
- Websites
- Social media platforms
- Mobile-friendly interfaces
Key Features of Breezy News
1. Fast and Fresh Updates
Breezy News focuses on delivering news as it happens, ensuring readers stay current.
2. Easy-to-Read Format
Short paragraphs and simple language make content accessible to all readers.
3. Wide Content Variety
From local updates to global trends, the platform covers diverse topics.
4. Mobile Optimization
Designed for users who consume news on smartphones and tablets.
Why Breezy News is Gaining Popularity
Several factors contribute to its growing appeal:
- Quick and digestible content
- Focus on relevant and trending topics
- Strong presence on social media
- User-friendly reading experience
In an age of information overload, platforms like Breezy News provide a refreshing alternative.
Role in Modern Digital Media
Breezy News reflects the shift toward:
- Short-form journalism
- Real-time reporting
- Audience-focused storytelling
It aligns with how modern readers prefer to consume news—quickly, clearly, and on-the-go.
Benefits of Using Breezy News
Saves Time
Readers can stay informed without reading lengthy articles.
Easy Accessibility
Available across multiple devices and platforms.
Engaging Content
Designed to keep readers interested and informed.
Community Connection
Often highlights local stories that matter to readers.
Challenges Facing Platforms Like Breezy News
Despite its advantages, there are challenges:
- Balancing speed with accuracy
- Competing with larger media outlets
- Avoiding misinformation in fast reporting
- Maintaining credibility
Successful platforms must ensure fact-checking and responsible journalism.
How to Get the Most Out of Breezy News
To use the platform effectively:
- Follow official pages for updates
- Cross-check important news with reliable sources
- Engage with content for better recommendations
- Stay aware of trending topics
Conclusion
Breezy News represents the future of digital journalism—fast, accessible, and reader-focused. With its emphasis on fresh updates and simplified storytelling, it has become a go-to source for modern news consumers.
FAQ’s
1. What is Breezy News?
Breezy News is a digital news platform that provides quick and easy-to-read updates on current events and trending topics.
2. Is Breezy New’s reliable?
It aims to provide timely information, but readers should verify important news from multiple trusted sources.
3. What type of content does Breezy New’s cover?
It covers breaking news, local updates, lifestyle topics, and trending stories.
4. How can I access Breezy New’s?
You can access it through its website, social media platforms, and mobile devices.
5. Why is Breezy New’s popular?
Its short, engaging, and mobile-friendly content makes it appealing to modern readers.
BLOG
Unraveling the Mysteries of Chainiste: A Comprehensive Guide

Introduction
The term Chainiste is not widely defined in mainstream dictionaries, yet it has begun appearing in various online discussions, niche communities, and conceptual frameworks. Whether used in technology, philosophy, or branding, Chainiste carries an air of mystery that sparks curiosity.
This guide explores what Chainiste could mean, where it might come from, and how it is being interpreted in modern contexts.
What is Chainiste?
At its core, Chainiste appears to be a conceptual or emerging term rather than a strictly defined word. It is often interpreted in multiple ways depending on context.
Possible Interpretations
- A person or system connected to chains or networks
- A philosophy centered on interconnected systems
- A digital or blockchain-related concept
- A brand or identity built around connectivity
Because the term lacks a fixed definition, it is considered flexible and evolving.
Etymology and Origins
The word “Chainiste” likely derives from:
- “Chain” – representing connection, sequence, or linkage
- “-iste” – a suffix often used to describe a follower, specialist, or practitioner
Together, the term could suggest “one who works with or believes in chains or interconnected systems.”
Chainiste in Technology
One of the most common interpretations of Chainiste is in the tech world, especially linked to Blockchain.
Possible Tech Meanings
- A blockchain enthusiast or expert
- A developer working with decentralized systems
- A supporter of distributed ledger technology
In this sense, a Chainiste might represent someone deeply involved in modern digital infrastructure and decentralized innovation.
Chainiste as a Philosophy
Beyond technology, Chainiste can also be viewed as a philosophical concept.
Core Ideas
- Everything is interconnected
- Actions create chains of consequences
- Systems influence one another continuously
This aligns with broader ideas found in systems thinking and network theory.
Chainiste in Digital Culture
In online communities, Chainiste may be used as:
- A username or identity
- A niche community label
- A conceptual brand name
It reflects modern internet culture where new terms emerge organically and gain meaning through usage rather than formal definition.
Applications of the Chainiste Concept
1. Technology & Innovation
Used to describe professionals working in blockchain or network systems.
2. Business & Branding
Companies may adopt the term to represent connectivity and modern thinking.
3. Philosophy & Thought Leadership
Represents interconnected thinking and systemic awareness.
4. Creative Fields
Writers and creators may use it symbolically to represent relationships and continuity.
Why Chainiste is Gaining Attention
Several factors contribute to its rising interest:
- Growth of blockchain and decentralized systems
- Increased focus on interconnected digital ecosystems
- Curiosity around unique and modern terminology
- Branding appeal due to its futuristic tone
Challenges in Defining Chainiste
Despite its appeal, the term faces limitations:
- No official or standardized definition
- Multiple interpretations leading to confusion
- Lack of academic or institutional recognition
This makes it more of a conceptual keyword than a formal term.
Future of Chainiste
The future of Chainiste depends on how it is adopted:
- It could become a recognized term in tech communities
- It may evolve into a brand or movement
- It could remain a niche concept with flexible meaning
Like many modern digital terms, its value lies in how people use and define it over time.
Conclusion
Chainiste is a fascinating example of how language evolves in the digital age. Whether viewed through the lens of Blockchain, philosophy, or branding, it represents the idea of connection and interconnected systems.
FAQ’s
1. What does Chainiste’s mean?
Chainiste’s is an emerging term often associated with interconnected systems, blockchain, or conceptual philosophies.
2. Is Chainiste a real word?
It is not officially defined in dictionaries but is used in niche and digital contexts.
3. Is Chainiste related to blockchain?
Yes, it is often interpreted as being connected to blockchain and decentralized technologies.
4. Can Chainiste be used as a profession?
Informally, it could describe someone working with network systems or blockchain technologies.
5. Why is Chainiste gaining popularity?
Its modern, flexible meaning and connection to digital innovation make it appealing in online communities.
BLOG
Vivek Mehra: A Visionary Leader’s Journey

Introduction
Vivek Mehra stands out as a dynamic leader whose career spans corporate leadership, entrepreneurship, education, and thought leadership. His journey reflects a blend of innovation, resilience, and a deep commitment to knowledge dissemination—making him a notable figure in the global publishing and education ecosystem.
Early Life and Educational Foundation
While detailed early-life records are limited publicly, Vivek Mehra’s academic and professional path reflects a strong foundation in business, leadership, and intellectual pursuits. His later engagement with law studies and a PhD in management highlights his continuous dedication to learning and growth.
Rise in Corporate Leadership
Leadership at SAGE Publications India
One of the most defining phases of his career was his role as:
- CEO and Managing Director
- Later Chairman
At SAGE Publications India, he played a key role in expanding academic publishing, fostering global collaborations, and strengthening access to scholarly content. His leadership contributed significantly to enhancing the reach of research publications in emerging markets.
Entrepreneurial Vision
Founder of Vikramshila Research Pvt Ltd
After a successful corporate career, Vivek Mehra transitioned into entrepreneurship by founding Vikramshila Research in 2023.
Key Goals of the Venture:
- Promote open-access research publishing
- Support scholars from developing countries
- Contribute to building a “knowledge-driven society”
This move highlights his vision of democratizing knowledge and making academic research more accessible worldwide.
Contributions Beyond Business
Thought Leadership and Mentorship
Vivek Mehra is more than a corporate executive. His contributions include:
- TEDx speaker, sharing insights on leadership and innovation
- Startup mentor, guiding emerging entrepreneurs
- Workshop trainer, focusing on publishing and ethics
Academic Engagement
He actively teaches research publishing and ethics to PhD students and continues to pursue his own doctoral studies, demonstrating his lifelong commitment to education.
Awards and Recognitions
His impactful work has earned him multiple accolades:
- Business Excellence and Innovative Best Practices Academia Award (2019)
- Sharda Top Rankers Excellence Award for Visionary Leadership (2016)
- Vijayshree Award (Government of Maharashtra, 1994) for simplifying agricultural technology
These awards reflect his contributions across industries—from publishing to technology and education.
Leadership Style and Philosophy
Key Traits
- Vision-driven thinking: Focused on long-term impact rather than short-term gains
- Commitment to learning: Continuously evolving through education and research
- People-centric leadership: Known for building teams and nurturing talent
He describes himself as a “rational optimist,” emphasizing balanced thinking and continuous discovery.
Impact on Publishing and Education
Vivek Mehra’s influence extends into:
- Expanding academic publishing in emerging economies
- Promoting ethical research practices
- Supporting global knowledge exchange
His work bridges the gap between traditional publishing and modern digital dissemination.
Personal Interests
Beyond his professional life, he is known for:
- Practicing yoga and squash
- Exploring philosophy and intellectual thought
- Writing and sharing perspectives through blogs
These interests contribute to his well-rounded leadership approach.
Challenges and Growth
Like many visionary leaders, Vivek Mehra’s journey includes:
- Navigating the shift from traditional to digital publishing
- Building a startup after a long corporate career
- Adapting to evolving global education systems
His ability to embrace change has been a key factor in his success.
Legacy and Future Outlook
With initiatives like Vikramshila Research, Vivek Mehra continues to:
- Champion open knowledge ecosystems
- Inspire future leaders and scholars
- Shape the future of global publishing
His journey reflects a commitment to making knowledge accessible and impactful on a global scale.
FAQ’s
1. Who is Vivek Mehra?
Vivek Mehra is an Indian publishing executive, entrepreneur, and founder of Vikramshila Research, known for his contributions to academic publishing.
2. What is Vivek Mehra known for?
He is best known for his leadership at SAGE Publications India and his work in promoting open-access research.
3. What is Vikramshila Research?
It is a research publishing platform founded by Vivek Mehra to make scholarly content accessible globally.
4. Has Vivek Mehra received any awards?
Yes, he has received multiple awards, including the Business Excellence Award and the Vijayshree Award.
5. Is Vivek Mehra involved in education?
Yes, he teaches research publishing and ethics and is pursuing a PhD in management.
6. What is his leadership style?
He is known for visionary, people-centric, and learning-driven leadership.
7. What is his current focus?
He is focused on expanding open-access publishing and mentoring the next generation of leaders.
Conclusion
Vivek Mehra exemplifies what it means to be a visionary leader in the modern era. From corporate success to entrepreneurial innovation, his journey highlights the power of knowledge, leadership, and continuous growth.
-

 TECH1 year ago
TECH1 year agoHow Cyber Security Services Help Organizations Manage Cyber Risk
-

 BLOG1 year ago
BLOG1 year agoSlothokiturbo.net: Exploring the World of Online Gaming and Community
-

 BLOG12 months ago
BLOG12 months agoLiteroticatags: Exploring the World of Erotica and Its Online Community
-

 TECHNOLOGY1 year ago
TECHNOLOGY1 year agoAagmal: The Future of Innovation and Efficiency
-

 BLOG1 year ago
BLOG1 year agoErothtos: Understanding Its Role in Today’s World 2025
-

 TECH1 year ago
TECH1 year agoMansrufer: Pioneering Progress in Technology
-
 FASHION12 months ago
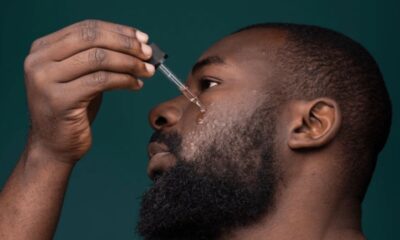
FASHION12 months agoAchieve the Perfect Beard with Black Male Beard Products
-

 BLOG1 year ago
BLOG1 year agoLeah Gettens: Everything You Need To Know