BLOG
Tubgirñ: Comprehending Its Importance and Uses

Amid rapidly evolving industries and advancing technologies, Tubgirñ is steadily emerging as a versatile and crucial tool. Its applications extend across various disciplines, making it a fundamental resource for businesses, researchers, and innovators seeking practical and efficient solutions.
But what exactly is Tubgirñ, and why does it matter? If you’re aiming to stay competitive and push boundaries, understanding the potential of Tubgirñ is critical. This article breaks down its significance, practical applications, and how it empowers organizations worldwide to innovate and thrive.
What Is Tubgirñ?
Tubgirñ is, at its essence, a cutting-edge system designed to streamline and enhance processes. Characterized by its precision, adaptability, and expansive capability, Tubgirñ’s operates as a multi-functional asset across various industries. With underlying principles founded on optimization and efficiency, Tubgirñ enables organizations to overcome complex challenges quickly and effectively.
By facilitating advanced methodologies, Tubgirñ’s helps professionals to break barriers, build innovative systems, and drive results in a manner unmatched by traditional approaches.
The Key Advantages of Tubgirñ’s
Professionals and organizations implementing Tubgirñ’s will uncover an array of significant benefits, many of which redefine how projects are executed. These benefits include:
- Unmatched Accuracy: Tubgirñ’s can achieve a level of precision that manually implemented systems struggle to match, reducing errors and enhancing outcomes.
- Scalability: Whether applied to a small-scale operation or an industry-spanning initiative, Tubgirñ’s adapts seamlessly to meet your specific needs.
- Efficiency Boost: By automating or streamlining complex tasks, Tubgirñ’s significantly reduces processing time, enabling teams to allocate resources toward innovation and growth.
- Cost-Optimization: Tubgirñ’s streamlines workflow, minimizes operational expenses, and maximizes resource utilization—driving higher ROI.
Industries Impacted by Tubgirñ’s
Tubgirñ’s has made its mark across a wide field of industries. Its capacity for practical, scalable applications has made it particularly indispensable in the following sectors:
1. Healthcare
Healthcare institutions benefit from Tubgirñ’s ability to streamline processes, such as clinical documentation, data management, and patient onboarding. For example, Tubgirñ’s aids in converting error-prone manual processes into seamless workflows, ensuring better patient care and improved compliance.
2. Finance
Financial institutions use Tubgirñ’s to enhance security, manage risk, and optimize financial transactions. Its precision significantly reduces inaccuracies in sensitive operations like auditing and regulatory compliance.
3. Logistics
Tubgirñ’s maximizes efficiency in supply-chain logistics. Whether managing inventory, forecasting demand, or routing deliveries, Tubgirñ’s ensures an optimal operational flow, reducing delays and associated costs.
4. Manufacturing
By enhancing production line efficiency and quality assurance protocols, Tubgirñ allows manufacturers to optimize workflows and improve product consistency significantly.
5. Education and Research
Educational bodies and research organizations utilize Tubgirñ to analyze data, maximize institutional performance, and even simulate experimental outcomes, all elevating the quality of knowledge gained.
How Tubgirñ Works—Simplifying Complex Challenges
Step 1: Deploy Custom Configurations
Tubgirñ adapts at its core to align with the organization’s goals. By assessing the intent and outcomes required, Tubgirñ’s system can be tailored for specific usage, ensuring maximum effectiveness.
Step 2: Implement Integration
Integration is seamless with existing systems, minimizing disruption during adoption. IT teams can deploy configurations without compromising current processes.
Step 3: Data Analysis and Execution
Upon integration, enterprises feed Tubgirñ with data required for successful operations. It leverages advanced analysis and algorithms to achieve desired results.
Step 4: Real-Time Adjustments
Tubgirñ continuously evaluates and optimizes its processes by identifying irregularities. With its real-time adaptability, decision-makers can implement changes dynamically as data evolves.
Real-World Applications Demonstrating Tubgirñ’s Potential
Case Study 1: Revolutionizing Healthcare Operations
A multi-specialty healthcare provider adopted Tubgirñ to expedite patient scheduling and improve electronic health records (EHR) management. Within six months, the institution recorded a 40% decrease in admin hours and a 25% increase in patient satisfaction rates.
Case Study 2: Transforming Logistics Efficiency
A leading supply-chain organization integrated Tubgirñ to optimize its delivery networks. By identifying inefficiencies in routing, the company cut fuel costs by 18% annually while significantly reducing overall delivery times.
Case Study 3: Innovative Research Outcomes
Universities seeking to simulate experimental responses deployed Tubgirñ for enhanced modeling accuracy. The resulting simulations allowed researchers to predict outcomes with a 50% greater accuracy, accelerating their projects significantly.
Why Tubgirñ Is Essential for Future-Forward Enterprises
1. Adopting AI and Automation
Businesses striving for innovation and automation must adopt tools like Tubgirñ. Incorporating these systems creates opportunities for meaningful transformation that aligns with modern demands.
2. Thriving Amid Competition
By enabling measurable efficiency, Tubgirñ offers organizations a significant competitive advantage in rapidly evolving landscapes.
3. Resilience in an Uncertain World
Tubgirñ empowers organizations to remain adaptive—ensuring resilience, regardless of future disruptions or challenges.
Unleash the Potential of Tubgirñ Today
Understanding and utilizing Tubgirñ in your operations provides the unique opportunity to revolutionize your existing workflows. Whether you’re leading advancements in healthcare, calculations in finance, or breakthroughs in research, Tubgirñ stands as an invaluable ally that drives not only results—but excellence.
Are you ready to elevate your organization’s success with Tubgirñ? Don’t wait—connect with us to unlock unparalleled potential!
BLOG
IGsty.com: Free Instagram Photo, Story, and Reels Downloader Tool
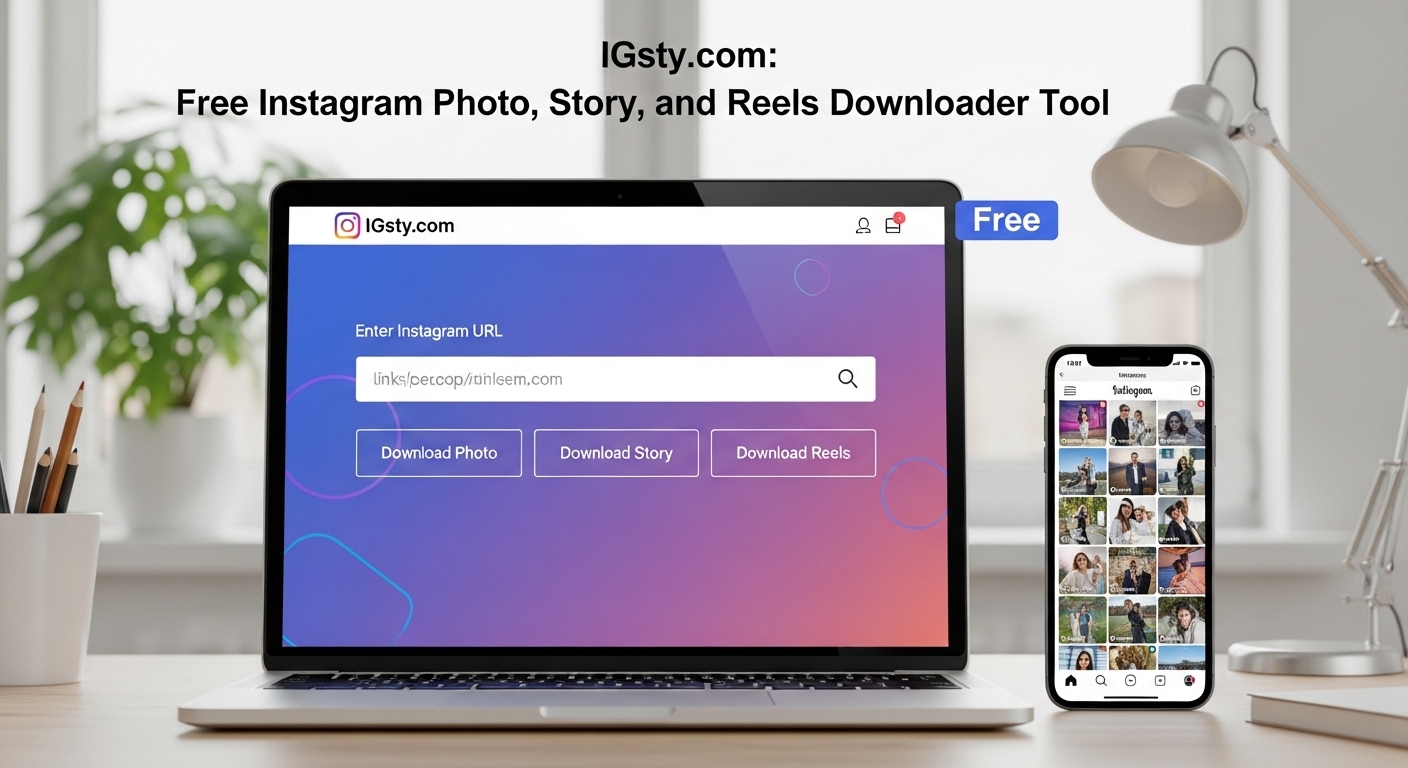
IGsty.com is a web-based tool concept commonly associated with downloading Instagram photos, stories, reels, and videos without requiring a mobile app. It fits into a broader category of online utilities designed to help users save publicly available social media content for offline viewing.
What Is IGsty.com?
IGsty.com is typically described as an online Instagram downloader tool that allows users to:
- Download Instagram photos
- Save Instagram stories
- Download reels and short videos
- Access media without installing software
It works through a browser interface where users paste a content link to retrieve downloadable media.
How Instagram Download Tools Work
Tools like IGsty.com function using public data retrieval methods:
1. Link Input
Users copy an Instagram post link and paste it into the tool.
2. Media Extraction
The system reads publicly available media from Instagram’s servers.
3. File Processing
Images or videos are converted into downloadable formats.
4. Download Option
Users can save content directly to their device.
This process interacts with platforms like Instagram, which is owned by:
Meta Platforms
Features Commonly Associated with IGsty.com
1. Photo Downloader
Allows saving high-quality Instagram images.
2. Story Saver
Enables downloading temporary Instagram stories before they expire.
3. Reels Downloader
Supports saving short-form video content.
4. No App Required
Works directly in a web browser.
5. Free Access
Most similar tools are free to use.
Why People Use Instagram Downloader Tools
Users typically use tools like IGsty.com for:
- Saving inspirational content
- Archiving personal favorite posts
- Offline viewing
- Content research or reference
- Reposting (where legally allowed)
Legal and Ethical Considerations
While these tools are widely used, there are important considerations:
- Downloading copyrighted content without permission may violate rules
- Instagram’s terms of service restrict unauthorized content redistribution
- Users should only download content they own or have permission to use
Ethical use is important when dealing with social media content.
Safety Considerations
When using any online downloader tool, users should be cautious:
- Avoid suspicious ads or pop-ups
- Do not enter personal Instagram credentials
- Use trusted and secure websites
- Be careful of phishing-style clones
Advantages of IGsty-Type Tools
- Easy access without installation
- Fast media downloads
- Supports multiple content types
- Useful for content creators and researchers
- Works across devices
Limitations
- Cannot access private accounts
- May stop working if Instagram changes its system
- Possible legal restrictions depending on usage
- Quality depends on original upload
Alternatives in the Same Category
Other tools with similar functions include:
- Instagram web save tools
- Browser extensions for media downloading
- Mobile-based downloader apps
- Content archiving platforms
FAQ’s
1. What is IGsty.com used for?
It is used to download Instagram photos, stories, and reels from public posts.
2. Do I need an account to use it?
No, most versions of such tools do not require login.
3. Can it download private posts?
No, it typically only works with public content.
4. Is it safe to use?
Generally yes for browsing, but users should avoid entering personal login details.
5. Is downloading Instagram content legal?
It depends on usage and copyright rules; permission is required for reuse or redistribution.
Conclusion
IGsty.com represents a category of online tools designed to simplify access to Instagram media by enabling downloads of photos, stories, and reels. While convenient for personal use and content reference, it must be used responsibly, respecting copyright laws and platform policies set by Meta Platforms.
BLOG
MagFuseHub.com: A Multi-Niche Information Hub for Modern Readers
BLOG
Puzutask.com: A Smart Platform for Task Management

In a world where productivity tools are essential for both individuals and teams, Puzutask.com is presented as a modern task management platform designed to help users organize work, improve efficiency, and manage daily responsibilities in a structured way.
It reflects the growing demand for simple yet powerful digital tools that make planning and execution easier in both personal and professional environments.
What is Puzutask.com?
Puzutask.com is a digital task management platform that allows users to create, track, and organize tasks in one centralized system. It is designed to help users stay productive by breaking work into manageable steps and providing a clear overview of progress.
The platform typically focuses on:
- Task creation and scheduling
- Priority-based organization
- Progress tracking
- Team collaboration features (in some versions)
Key Features of Puzutask.com
1. Task Organization
Users can create tasks, assign deadlines, and categorize them based on priority or project type.
2. Simple Interface
The platform is designed to be clean and easy to use, reducing complexity for everyday task management.
3. Progress Tracking
Users can monitor completed and pending tasks in real time, helping improve productivity awareness.
4. Reminder System
Notifications and reminders help ensure important tasks are not missed.
5. Cloud-Based Access
Being online-based, users can access their tasks from multiple devices.
How Puzutask.com Helps Users
Improves Productivity
By organizing tasks clearly, users can focus on what matters most.
Reduces Mental Load
Instead of remembering everything, users rely on a structured system.
Enhances Time Management
Deadlines and scheduling tools help users manage their time effectively.
Supports Collaboration
If team features are available, users can coordinate tasks more efficiently.
Common Use Cases
Personal Task Management
- Daily to-do lists
- Habit tracking
- Study planning
Business Use
- Project management
- Team assignments
- Workflow tracking
Freelancers
- Client task tracking
- Deadline management
- Project organization
Benefits of Using Puzutask.com
- Easy-to-use productivity system
- Centralized task tracking
- Better organization of work and goals
- Reduced missed deadlines
- Improved workflow clarity
Comparison with Other Tools
Compared to platforms like Trello, which use board-based task organization, Puzutask.com appears to focus on a simpler, streamlined task list approach.
Unlike more complex systems such as Asana, it may appeal more to users who prefer minimal setup and quick task entry rather than advanced project structuring.
Possible Limitations
While useful, task management platforms like Puzutask.com may have limitations such as:
- Limited advanced project management features
- Fewer integrations with third-party tools
- Basic reporting or analytics options
- Dependence on internet access
Future of Task Management Platforms
The future of platforms like Puzutask.com is expected to include:
- AI-powered task suggestions
- Smart scheduling based on behavior patterns
- Voice-based task creation
- Deeper integration with workplace tools
- Automated productivity insights
These advancements aim to make task management more intuitive and proactive.
Conclusion
Puzutask.com represents a modern approach to task management by focusing on simplicity, organization, and accessibility. While it may not replace advanced enterprise tools, it offers a practical solution for users who want a straightforward way to manage daily tasks and improve productivity.
FAQ’s
1. What is Puzutask.com used for?
It is used for creating, organizing, and tracking tasks in a structured way.
2. Is it suitable for teams?
It may support team use depending on available features, but it is also suitable for individuals.
3. Does it require installation?
It is typically web-based, so it can be accessed through a browser.
4. Is it better than Trello or Asana?
It depends on user needs—Puzutask.com is more likely focused on simplicity, while others offer advanced features.
5. Can I use it for personal planning?
Yes, it is well-suited for daily to-do lists and personal productivity.
-

 TECH12 months ago
TECH12 months agoHow Cyber Security Services Help Organizations Manage Cyber Risk
-

 BLOG1 year ago
BLOG1 year agoSlothokiturbo.net: Exploring the World of Online Gaming and Community
-

 BLOG11 months ago
BLOG11 months agoLiteroticatags: Exploring the World of Erotica and Its Online Community
-

 BLOG1 year ago
BLOG1 year agoErothtos: Understanding Its Role in Today’s World 2025
-

 BLOG1 year ago
BLOG1 year agoWatchmenontheall Calvin: An Exploration of Themes, Characters, and Significance
-
 FASHION11 months ago
FASHION11 months agoAchieve the Perfect Beard with Black Male Beard Products
-

 BLOG1 year ago
BLOG1 year agoLeah Gettens: Everything You Need To Know
-

 TECH1 year ago
TECH1 year agoMansrufer: Pioneering Progress in Technology

